by Paul Matthews, CEO
The software as a service (SaaS) revolution has made it incredibly easy to roll out new applications across an organisation or supply chain.
It means that workers can gain instant access to tools to help them do their work, boosting their productivity in the process. But there’s a flipside to that coin - application sprawl.
It’s become particularly pronounced since the rush to cloud services and apps spurred by the arrival of Covid-19. Each department in a typical large enterprise now runs 200 applications. The plethora of new generative AI apps being offered to streamline everything from accounting reconciliations to graphic design is only going to see more apps deployed.
Many of these apps don’t go anywhere near the IT department - they are adopted by frontline business users who need only sign up for a subscription. So businesses are increasingly reliant on those SaaS providers to build top-notch security into their software.
And hope for no hacks that affect their supply chain security.
The SolarWinds Hack
The problem is that software makers are in an arms race with increasingly sophisticated hackers, and the good guys are losing. While network security teams do their best to monitor devices and networks and train staff to spot phishing attempts, breaches resulting from vulnerabilities in third-party software are becoming common.
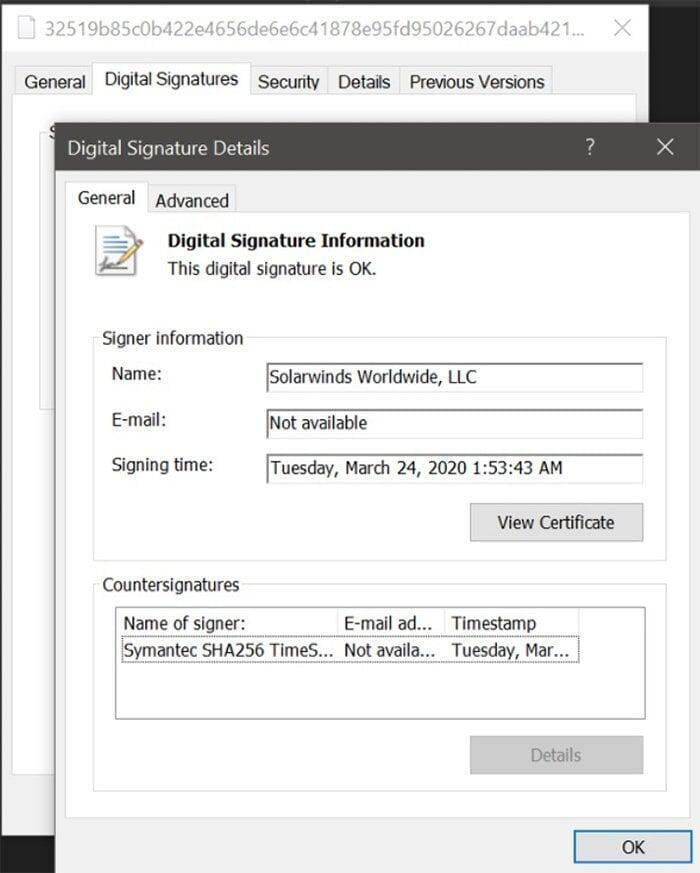
The most infamous example in recent years was the SolarWinds hack of 2020.
The Texas-based developer of network monitoring tools had over 30,000 customers globally when it sent out an innocuous software update to its Orion tool in March, 2020. Unfortunately, SolarWinds had been infiltrated by hackers months earlier and its software updates downloaded by clients included malware.
It led to a number of US government agencies and major corporations, Microsoft and Cisco included, having their networks compromised. As end-point and network security is tightened up, hackers are realising that it's easier to try and hijack the process of software development, testing and delivery instead, piggybacking on or masquerading as a trusted partner.
Secure by design?
The governments of the US, New Zealand, Australia, Canada and Germany are so concerned about software supply chain hacks that they’ve published new guidelines urging software makers to adopt ‘secure by design’ and ‘secure by default’ design principles. The European Union is going a step further, introducing the Cyber Resilience Act to require software and digital service providers to meet minimum security standards.
Such moves directly target hacking techniques including malicious code injection, fake software updates, and compromising software building systems. Software makers will indignantly argue that security is top of mind for them. The last thing they want is to be responsible for their customers’ suffering data breaches and service disruption.
But they also face overwhelming competitive pressure to add new features and innovative services. Too often, security is sidelined in favour of speed to market.
The rise of generative AI systems is a double-edge sword when it comes to security. Services like Microsoft Security Copilot will help automate more security monitoring and threat detection processes. But the hackers are also employing AI to automate their attacks.
So what are company leaders and their IT teams supposed to do in this increasingly complicated and risky cybersecurity landscape?
Here are five tips to minimising the prospects of being caught up in software supply chain hacks:

1. Do basic security well:
This includes using strong authentication, encryption, and access controls to protect against unauthorised access and tampering. A supply chain hack may be successful in depositing malware onto your company network. But more often than not, the hack will also require lax processes around authentication and access controls to take effect. Having good basic security hygiene limits the chances of data breaches and unauthorised access, even if a software provider does let you down.

2. Monitor for suspicious activity:
Organisations should monitor their software supply chains for any suspicious activity, such as unauthorised access or changes to code, which could signal there have been hacks. A good software partner should be responsive to queries about suspicious activity, too.
Organisations can implement a combination of automated tools and manual reviews of code changes, access logs, and other relevant data sources to detect and investigate potential security incidents.

3. Conduct regular security audits:
Regular security audits can help identify vulnerabilities in the software supply chain and address them before they can be exploited. This should go for apps frontline business users are deploying, particularly if they draw on company data via APIs (application programming interfaces) etc.

4. Verify software updates:
Users should always verify that software updates are legitimate before installing them, by checking for digital signatures or other indicators of authenticity. Updates should only be downloaded from official, verified sources. This is particularly important for open source software applications, which may be offered from multiple sources on the web.

5. Support secure design:
Software makers usually talk up the great features of their applications rather than the security underpinning them. It's your job to drill a bit deeper, looking into security. You have the ability to influence software development practices by supporting developers that adopt secure by design and -default principles.
Contact CIO Studio for advice on how to implement best practice cybersecurity management for the third-party applications and services you are using.